OpenClaw is an open-source AI gateway that connects messaging apps like Telegram, Discord, WhatsApp, and Slack with advanced language models such as GPT-4 and Claude 4. By hosting it on a VPS, you can ensure your AI agent runs 24/7, making it ideal for tasks like automated trading workflows, automations, and real-time data monitoring. Here's a quick breakdown of what you'll need and how to get started:
- VPS Requirements: At least 2GB RAM (4GB recommended), 2 vCPUs, and NVMe SSD storage for better performance.
- Operating System: Use Ubuntu 22.04 or 24.04 LTS for stability.
- Key Tools: Node.js 22+, Docker, Traefik, and an AI provider API key (e.g., OpenAI or Anthropic).
-
Setup Steps:
- Secure your VPS with SSH keys, a firewall, and user permissions.
- Install OpenClaw using the installer script.
- Configure Docker and Traefik for container management and reverse proxying.
- Customize OpenClaw settings for trading workflows and secure access.
Preparing Your QuantVPS for OpenClaw Installation
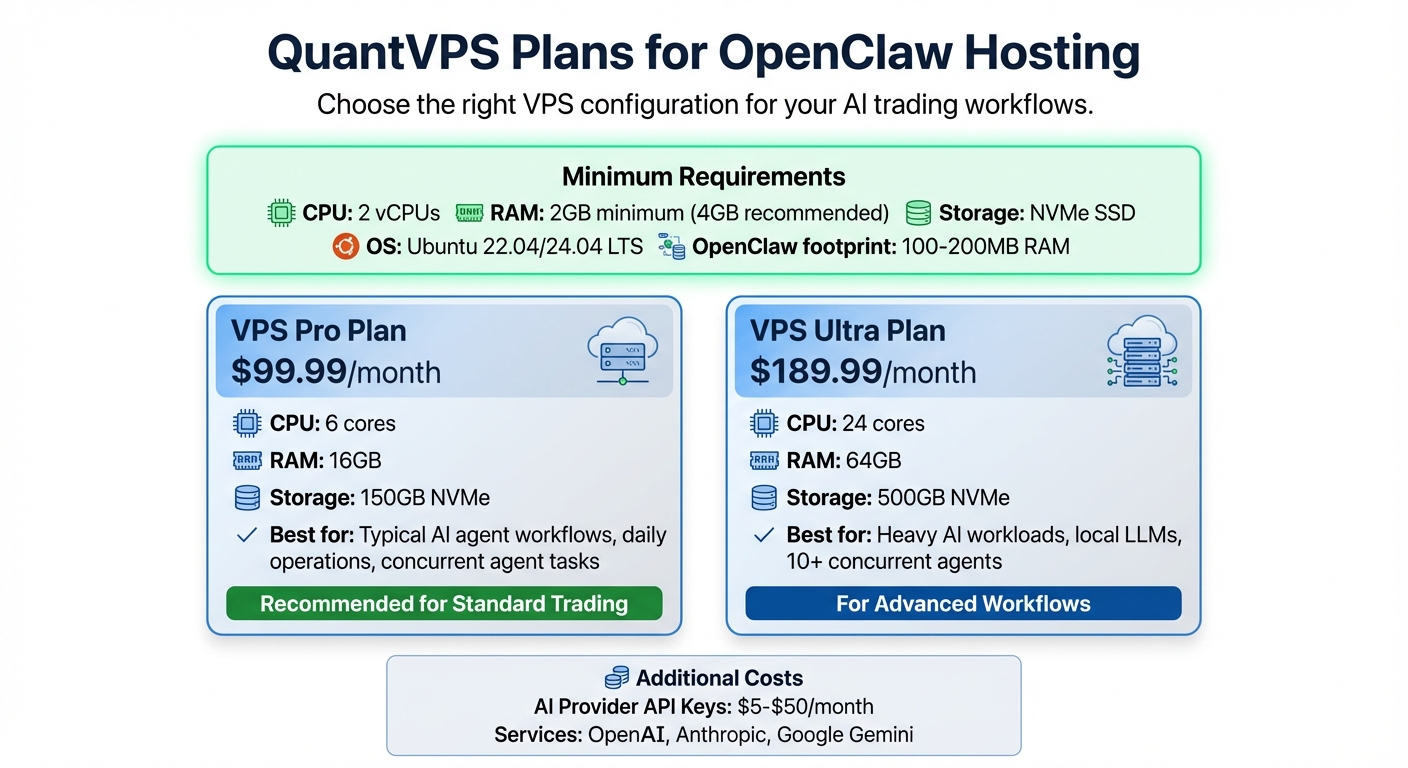
QuantVPS Plans Comparison for OpenClaw AI Gateway Hosting
Choosing the Right QuantVPS Plan
OpenClaw itself requires just 100–200MB of RAM, but you'll need at least 2GB (4GB is better) to accommodate Node.js overhead, logs, media processing, and handling multiple channels.
For CPU, starting with 2 vCPUs is sufficient for steady daily operations and managing concurrent agent tasks. When it comes to storage, go for NVMe SSDs instead of standard SATA drives - this drastically improves model loading times and overall responsiveness.
If you're looking for a solid option, the VPS Pro plan at $99.99/month (6 cores, 16GB RAM, 150GB NVMe) offers a great balance for typical AI agent workflows. For those tackling heavy AI workloads, running local LLMs, or managing more than 10 concurrent agents, the VPS Ultra plan at $189.99/month (24 cores, 64GB RAM, 500GB NVMe) is a better fit.
Keep in mind, you'll also need to budget an extra $5–$50 per month for AI provider API keys.
Initial VPS Configuration
Start by choosing Ubuntu 22.04 LTS or 24.04 LTS as your operating system - these versions are the most reliable for OpenClaw. Debian 11 and 12 are also good alternatives. Once your VPS is provisioned, log in via SSH and update the system with:
sudo apt update && sudo apt upgrade -y
Next, create a dedicated non-root user to enhance security:
adduser openclawops
usermod -aG sudo openclawops
Switch to this new user for all further steps in the installation process.
To secure SSH access, generate an ED25519 key using ssh-keygen -t ed25519 and copy it to your VPS with ssh-copy-id user@vps-ip. Then, disable password logins by editing the SSH configuration file (/etc/ssh/sshd_config) and setting PermitRootLogin no and PasswordAuthentication no.
Configure the firewall using UFW to block all incoming traffic except for SSH:
sudo ufw default deny incoming
sudo ufw limit 22/tcp
sudo ufw enable
The limit option helps slow down brute-force attacks by rate-limiting SSH connections.
Finally, enable "user lingering" to ensure your AI agent remains active even after you log out of SSH:
sudo loginctl enable-linger $USER
As Florian Darroman explains:
Without [enabling lingering], your agent dies the moment you close your terminal. With it, the agent persists forever.
With these steps, your VPS is now secured and ready for the next phase.
Prerequisites Checklist
Before diving into the OpenClaw installation, make sure you have the following:
- AI Provider API Key: Get this from Anthropic (Claude), OpenAI (GPT-4), or Google (Gemini).
- Messaging Platform: Obtain a Telegram Bot Token from @BotFather.
- Node.js 22+: This is mandatory for OpenClaw to function properly.
- Domain Name (optional): Needed if you're using Nginx with SSL; otherwise, SSH tunneling works for accessing the dashboard.
If your VPS only has 2GB of RAM, you'll need to manually add at least 2GB of swap space to avoid memory-related issues during installation. To check your Node.js version, run node --version. If it’s not installed or is below version 22, use Node Version Manager (nvm) to install the correct version.
With these preparations complete, you're ready to move forward with setting up OpenClaw.
Step-by-Step Guide to Install OpenClaw on a VPS
Running the OpenClaw Installer
To get started, log in to your VPS using SSH as a non-root user and execute the following command:
curl -fsSL https://openclaw.ai/install.sh | bash
NEVER MISS A TRADE
Your algos run 24/7
even while you sleep.
99.999% uptime • Chicago, New York, London & more data centers • From $59.99/mo
This command launches an interactive onboarding wizard that simplifies the setup process. First, you'll select QuickStart mode for an automated configuration. Then, choose your AI provider from Anthropic (Claude), OpenAI (GPT-4), or Google Gemini. Enter your API key and select the AI model you prefer. For trading workflows, the recommended option is Claude Opus 4.6 (anthropic/claude-opus-4-6) due to its advanced reasoning capabilities.
Next, configure a communication channel by providing either your Telegram Bot Token (generated via @BotFather) or a Discord webhook URL. To ensure OpenClaw runs continuously, enable the systemd daemon. Once the script completes, confirm the service is active by running:
openclaw gateway status
With the installer complete, the next step is to configure Docker and Traefik for container management.
Setting Up Docker and Traefik
After finishing the initial setup, you can deploy OpenClaw using Docker. Begin by installing Docker Engine 24+ and Compose v2:
curl -fsSL https://get.docker.com | sh
sudo usermod -aG docker $USER
Log out and back in to apply the group changes. Then, create a dedicated proxy network for secure container routing:
docker network create proxy
Now, set up Traefik for reverse proxying. Create a docker-compose.yml file in /opt/traefik with configurations for Let's Encrypt and volume mounts for /var/run/docker.sock and /letsencrypt. Deploy Traefik using:
docker compose up -d
If your VPS has only 2GB of RAM, create a 2GB swap file to prevent memory issues:
sudo fallocate -l 2G /swapfile
sudo chmod 600 /swapfile
sudo mkswap /swapfile
sudo swapon /swapfile
Deploying OpenClaw Containers
With Docker and Traefik ready, the next step is deploying OpenClaw containers. Start by cloning the OpenClaw repository and navigating to its directory:
git clone https://github.com/openclaw/openclaw.git
cd openclaw
Edit the docker-compose.yml file to include necessary environment variables. Make sure to set OPENCLAW_GATEWAY_TOKEN and your API keys. For persistent data storage, map the following volumes:
-
~/.openclaw:/home/node/.openclawfor configuration files -
~/.openclaw/workspace:/home/node/.openclaw/workspacefor agent data
To secure domain routing with Traefik, add labels to the OpenClaw service. These should include traefik.enable=true, a Host rule for your domain, and the load balancer port set to 18789. Important: Bind the port to 127.0.0.1:18789 to restrict public access and safeguard your trading operations.
Before you deploy, ensure the host directory permissions are correct:
sudo chown -R 1000:1000 ~/.openclaw
Finally, deploy the containers using:
docker compose up -d
You can verify that everything is running smoothly by checking the container status:
docker compose ps
If the openclaw-gateway status shows "Up", you're good to go. For troubleshooting, run:
openclaw doctor --fix
This command will automatically diagnose and resolve any configuration issues.
Customizing OpenClaw for Trading AI Workflows
Once you've deployed OpenClaw, the next step is tailoring its configuration to meet the demands of your trading workflows. This involves adjusting key settings, securing credentials, and ensuring the system runs smoothly under all conditions.
Editing Configuration Files
OpenClaw's main settings are stored in openclaw.json (found at ~/.openclaw/openclaw.json), while sensitive credentials are kept in a .env file. For trading-specific setups, you'll need to tweak both files to enhance security and performance.
-
Secure the Gateway: Update
openclaw.jsonto bind the gateway to127.0.0.1. This prevents external access. Use an SSH tunnel to access the UI remotely:ssh -L 18789:127.0.0.1:18789 user@your-vps-ip -
Authentication Token: Ensure the proper token path is set. OpenClaw's dashboard requires
gateway.auth.token(notgateway.token). Use a strong token value to secure API access. -
Optimize Startup: Add the following lines to your
.envfile for faster startup, especially on low-spec VPS setups:NODE_COMPILE_CACHE=/var/tmp/openclaw-compile-cache OPENCLAW_NO_RESPAWN=1
One quirk of OpenClaw is that it rewrites openclaw.json on startup, stripping away custom settings. As Sre Chakra Yeddula explains:
STOP LOSING TO LATENCY
Execute faster than
your competition.
Sub-millisecond execution • Direct exchange connectivity • From $59.99/mo
OpenClaw rewrites openclaw.json on startup and strips custom settings... After the gateway finishes its startup config touch (~10s), we overwrite the file with our known-good 'golden' copy.
To work around this, create a "golden config" backup of your customized openclaw.json. Then, use a cron job or startup script to restore this backup after the initial 10-second startup window.
Once your configuration is locked in, you'll want to ensure uninterrupted operation by setting up an auto-restart service.
Setting Up Auto-Restart Services
For 24/7 trading operations, it's critical to have OpenClaw restart automatically after crashes or system reboots. This can be achieved by creating a systemd service. Here's how:
-
Create a new service file at
/etc/systemd/system/openclaw.service:
Replace[Unit] Description=OpenClaw Trading Agent After=network.target [Service] Type=simple User=youruser WorkingDirectory=/home/youruser ExecStart=/usr/bin/node /home/youruser/openclaw/index.js Restart=always RestartSec=2 Environment="NODE_COMPILE_CACHE=/var/tmp/openclaw-compile-cache" Environment="OPENCLAW_NO_RESPAWN=1" [Install] WantedBy=multi-user.targetyouruserwith your actual username and adjust theExecStartpath to match your OpenClaw installation. -
Enable the service to start on boot and launch it immediately:
Thesudo systemctl enable openclaw sudo systemctl start openclawRestart=alwaysdirective ensures the service recovers from failures, whileRestartSec=2minimizes downtime by retrying every 2 seconds. -
If you're running OpenClaw as a non-root user, execute the following to keep the process alive even after your SSH session ends:
sudo loginctl enable-linger $USER -
Monitor logs in real-time to verify the auto-restart functionality:
journalctl -u openclaw -f
Integrating with Trading Tools
With OpenClaw secured and automated, you can now integrate it with your trading tools to streamline operations.
-
Workspace Volumes: OpenClaw's workspace directory (
~/.openclaw/workspace) is persistent across container restarts. Use it to store trading logs, strategy configurations, and session history. For example, you can maintain markdown files likePROJECTS.mdorHABITS.mdto track strategies and execution logs. OpenClaw can directly read and write to these files, eliminating the need for external databases. -
Install Trading Skills: Use the
clawdhubCLI to add plugins for market data feeds and execution systems. Install it globally first:
Then, search for and install relevant plugins. Enable these in thenpm i -g clawdhubplugins.entriessection ofopenclaw.json. -
Docker Configuration: For web-based trading interfaces or broker dashboards, include
shm_size: '2gb'in your Docker setup to prevent memory errors. Ensure your VPS has at least 2GB of RAM for basic operations; 4GB is better for multi-agent workflows handling real-time market data. This is especially useful for news-driven bots that require high-speed processing to trade breaking events.
Testing, Securing, and Troubleshooting Your OpenClaw Setup
Once you've tailored OpenClaw for your trading workflows, it's time to test its functionality, secure your VPS, and address any common issues that might arise.
Verification and Testing
After deploying your container, start by verifying everything is running smoothly. Use openclaw status to check gateway information and active sessions. If you're working with Docker, run docker ps to confirm that the openclaw-gateway container status is "Up." To catch and fix any configuration problems, execute openclaw doctor.
Access the Control UI by navigating to http://localhost:18789 in your browser. If you're on a remote VPS, set up an SSH tunnel with the following command: ssh -L 18789:127.0.0.1:18789 user@your-vps-ip. For real-time monitoring, use either docker logs -f openclaw or journalctl --user -u openclaw-gateway -f to keep an eye on logs for errors or access attempts. Verify that the process persists by checking lingering settings. Once testing is complete, focus on tightening security before addressing any issues.
Securing Your VPS
A study of 200 OpenClaw instances revealed that 96% were properly firewalled, and none operated without authentication. However, a Shodan scan conducted in February 2026 found 42,665 exposed instances, with 93.4% vulnerable due to misconfigurations. This highlights the importance of securing your setup, as OpenClaw's default settings can only do so much if manual errors occur.
Start by configuring UFW to block all incoming traffic except for port 22 (SSH). Install fail2ban to automatically block IPs after repeated failed login attempts. It's worth noting that automated bots often begin brute-force attacks within 15 minutes of a VPS going live, making these steps critical.
For OpenClaw itself, ensure the gateway is bound to 127.0.0.1 in the openclaw.json file. Avoid using 0.0.0.0, which leaves the service exposed to the internet. Use an SSH tunnel or tools like Tailscale for remote access instead of opening port 18789 in your firewall. Enable automatic security updates with unattended-upgrades, and regularly run openclaw security audit --fix to identify and resolve vulnerabilities. Finally, secure sensitive files like openclaw.json by setting permissions with chmod 600 ~/.openclaw/openclaw.json. These precautions help ensure your trading workflows remain secure.
Troubleshooting Common Issues
Even with careful setup, you might run into a few common problems. Here's how to address them:
-
Permission errors: These usually happen because the Docker container runs as UID 1000. Fix this by running
sudo chown -R 1000:1000 ~/.openclawto resolve volume mount issues. -
Port conflicts (EADDRINUSE): If port 18789 is already in use, find the conflicting process with
lsof -i :18789, then either terminate it or change the port inopenclaw.json. -
Out of Memory (OOM) errors: Low-cost VPS plans with 1GB–2GB of RAM can struggle. Add a 2GB swap file with
sudo fallocate -l 2G /swapfile && sudo chmod 600 /swapfile && sudo mkswap /swapfile && sudo swapon /swapfileto provide additional virtual memory. -
Unauthorized errors: Ensure the
OPENCLAW_GATEWAY_TOKENin your.envfile matches thegateway.auth.tokeninopenclaw.json. - Command not found: If commands fail, reconnect your SSH session to reload the PATH environment variable.
For a quick reference, here’s a summary of common issues and their solutions:
| Problem | Likely Cause | Solution |
|---|---|---|
| Permission Denied | Container UID mismatch | Run sudo chown -R 1000:1000 ~/.openclaw |
| EADDRINUSE | Port 18789 already taken | Kill the process with lsof -i :18789 or change the port in openclaw.json |
| Build Fails / "Killed" | Out of Memory (OOM) | Create a 2GB swap file using fallocate and mkswap |
| Unauthorized [undefined] | Missing/Wrong Gateway Token | Verify the token in .env matches the one in openclaw.json |
| Command Not Found | PATH not updated | Reconnect your SSH session |
| Agent stops on logout | Lingering disabled | Run sudo loginctl enable-linger $USER |
Conclusion
You've now completed the journey of deploying OpenClaw on a VPS. From picking the right QuantVPS plan to configuring your environment, deploying containers, and securing your setup, every step has been covered. Hosting OpenClaw on a QuantVPS ensures uninterrupted, round-the-clock reliability for your AI-driven trading workflows - sidestepping common issues like power outages or computer sleep modes that can disrupt local setups.
QuantVPS offers low-latency API connectivity to services like OpenAI and Anthropic, alongside NVMe storage for faster system responsiveness - both essential when dealing with real-time market signals that require split-second decisions. To maintain optimal performance, set up process managers like systemd or PM2 to automatically restart services after crashes or reboots. Keep your system updated by running commands like npm update -g openclaw or docker pull ghcr.io/openclaw/openclaw:latest for the latest features and security updates. Don’t forget to regularly back up your ~/.openclaw directory to protect your configurations and operational data.
Once you're comfortable with the basics, dive into advanced features like multi-agent setups, custom skills via clawdhub, or integrations with your existing trading tools. These additions can elevate the efficiency and security of your trading operations. With OpenClaw hosted on QuantVPS, you've built a resilient, high-performance foundation for your AI trading strategies. Features like VPS reliability, auto-restart services, and secure configurations work together to streamline your workflows. Just remember to keep your firewall settings tight, bind your gateway to localhost, and carefully scope your API keys - your trading success depends on it.
FAQs
Should I run OpenClaw with Docker or systemd?
Using Docker is often the preferred approach for running OpenClaw on a VPS. Why? Docker brings containerization to the table, which simplifies deployment and ensures a consistent environment - key for self-hosted, production-level setups.
Sure, you could use systemd to manage services on Linux, but Docker gives you more flexibility, better control over configurations, and enhanced privacy for AI workflows. That said, it’s worth noting that Docker does come with a learning curve and requires some regular upkeep to keep things running smoothly.
What’s the safest way to access the OpenClaw dashboard remotely?
To access the OpenClaw dashboard remotely in the safest way, stick to secure methods like SSH tunneling, reverse proxies with SSL, or VPNs. For personal use, SSH tunneling is a top choice because it encrypts your connection, keeping it secure. Make sure to avoid exposing the dashboard directly to the internet unless you're using proper authentication and encryption. This helps protect against unauthorized access and potential security risks.
How do I stop openclaw.json from being overwritten on startup?
To keep your openclaw.json file safe from being overwritten, avoid running the openclaw configure command multiple times, as it will rewrite the file each time. Instead, use commands like openclaw config set or openclaw config unset to make changes without risking a full rewrite.
Additionally, be aware that local models.json files in agent directories can override settings in openclaw.json. If this isn't desired, either disable these overrides or ensure changes are synced properly. To protect your configuration further, make it a habit to back up your openclaw.json file regularly. You can also implement safeguards, such as locking mechanisms, to prevent accidental overwrites.





